You Might Also Like
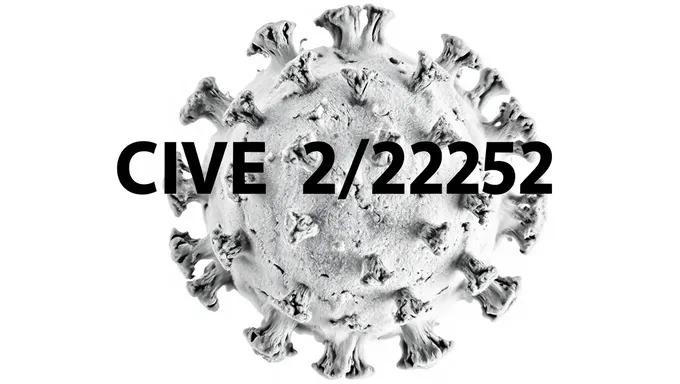
cve 2025 3661 (6,087)
Trending
Newest
- 1
- 2
- 3
- 4
- 203
© 2024 PixelHaha. All rights reserved.
English
English
Français
Português
日本語
Español
PixelHaha
Policies

Contact Us
support@pixelhaha.ai
Language
English
English
Français
Português
日本語
Español